Blog
Explore our latest insights, news, and updates.
Cryptography
Mar 13
8 min
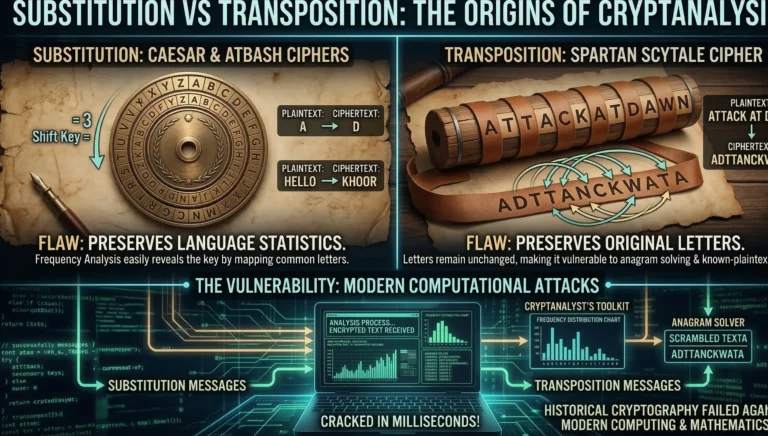
Substitution vs Transposition Cipher: 3 Devastating Historic Flaws
When analyzing the evolution of secure digital communications, modern engineers often overlook the foundational lessons of the past.…
Read More →
Cryptography
Mar 13
6 min
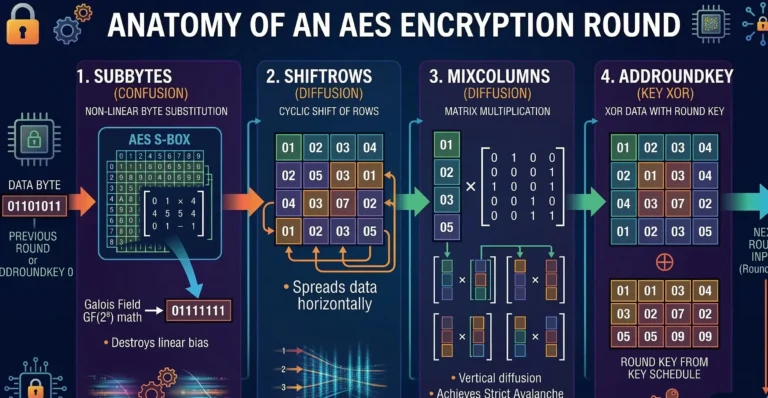
Differential Cryptanalysis: 5 Fatal Threats & Proven AES Defenses
Understanding differential cryptanalysis is the absolute pinnacle of modern cybersecurity engineering. In our previous modules, we explored how…
Read More →
Cryptography
Mar 13
8 min
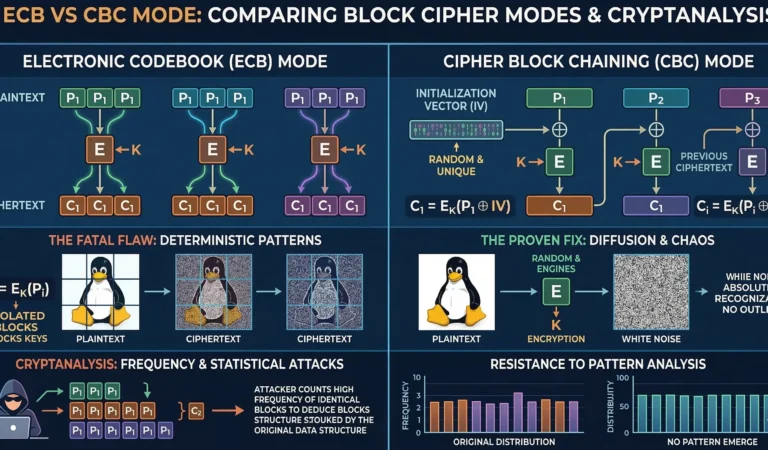
ECB vs CBC Mode: 5 Fatal Cryptanalysis Mistakes & Proven Fixes
Before diving into the deep statistical analysis of cryptographic vulnerabilities, we must understand a fundamental mathematical phenomenon known…
Read More →
Cryptography
Mar 12
7 min
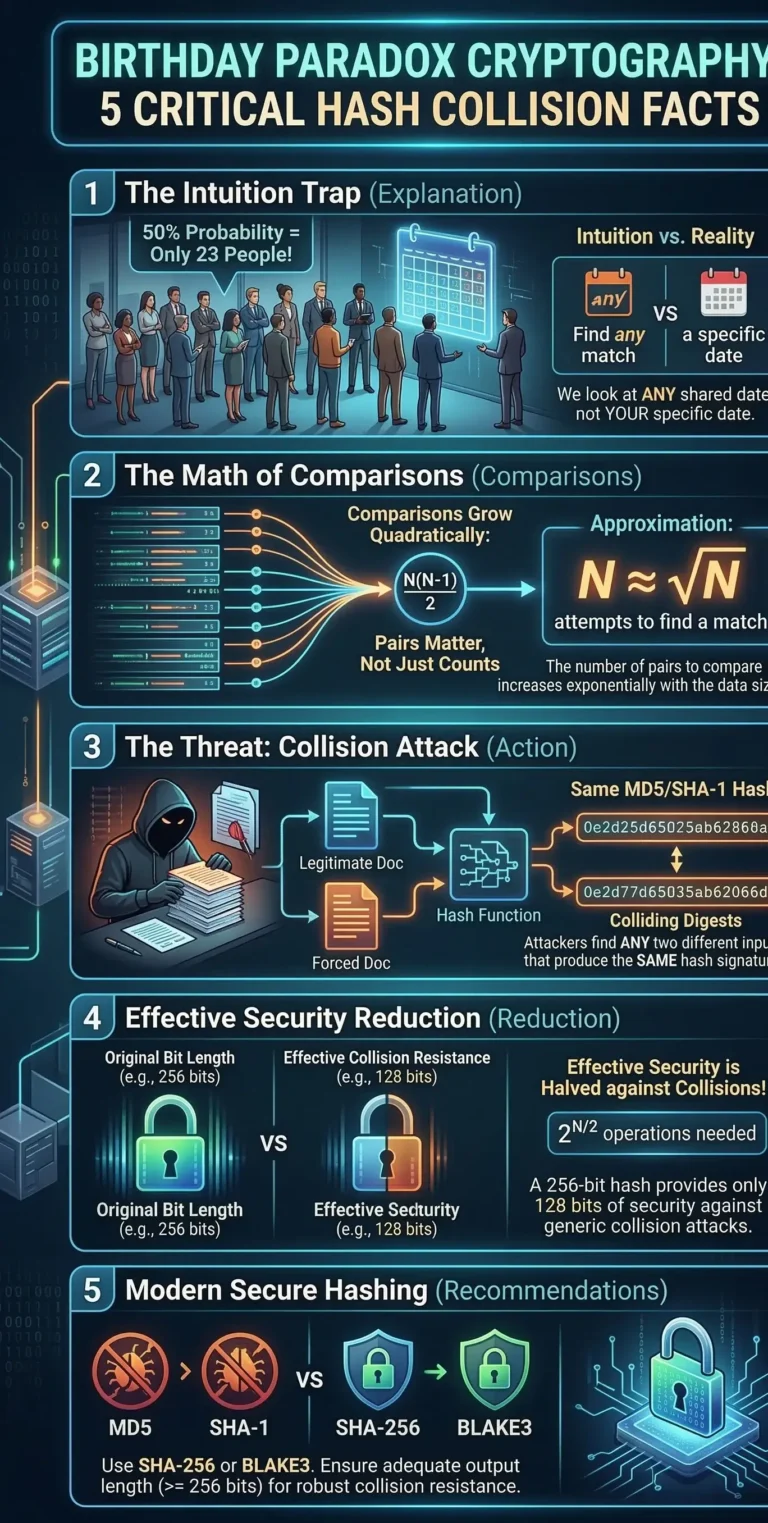
Birthday Paradox Cryptography: 5 Critical Hash Collision Facts
Birthday paradox cryptography is the absolute mathematical foundation for understanding how digital signatures, blockchain ledgers, and password storage…
Read More →
Cryptography
Mar 12
7 min
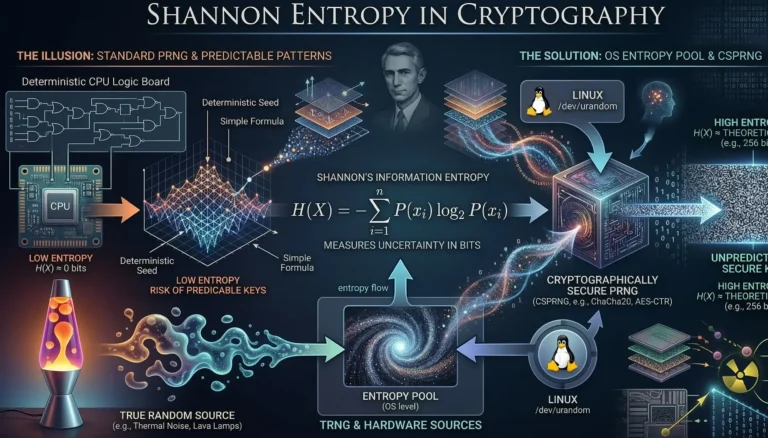
Shannon Entropy in Cryptography: 5 Critical Rules for Secure Keys
Understanding Shannon entropy in cryptography is not just an academic exercise; it is the absolute foundation of modern…
Read More →
Cryptography
Mar 10
9 min
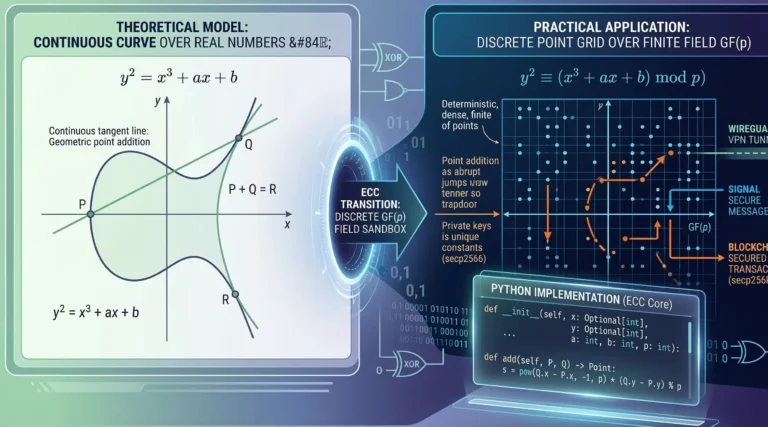
7 Brilliant Secrets of Elliptic Curve Cryptography & ECC
Finite Fields in Elliptic Curve Cryptography (ECC): From Theory to Practice Modern digital security is undergoing a fundamental…
Read More →